Last checked from Google Cloud Functions official status page 1 min. 31 sec. ago
Google Cloud Functions Status
Is Google Cloud Functions down?
Google Cloud Functions is up
Cloud computing services for business challenges by Google Cloud.
Not working for you?
StatusGator last checked the status of Google Cloud on and the service was operational. There have been 3 user-submitted reports of outages in the past 24 hours.
Google Cloud Functions service health
This chart represents Google Cloud Functions service health over the last 24 hours, with data points collected every 15 minutes based on issue reports, page visits, and signal strength. Sign up for free to see more Google Cloud Functions status data.
24 hrs ending
Top reported issues
View and upvote the most commonly reported Google Cloud Functions issues to help us better indicate the service status.
- Server not responding
- Connectivity issue
- Error message
- Sign in problem
- Service down
- Slow performance
- Unable to download
- App not loading
- Other
Have a different problem with Google Cloud Functions?
Recent outage reports
See recent outage reports from real Google Cloud Functions users
1 outage reports in the last 24 hours
Bucharest, Romania
"Chat sessions in Gemini Enterprise apps from EU multi-region are timing out. "
about 18 hours ago
about 18 hours ago
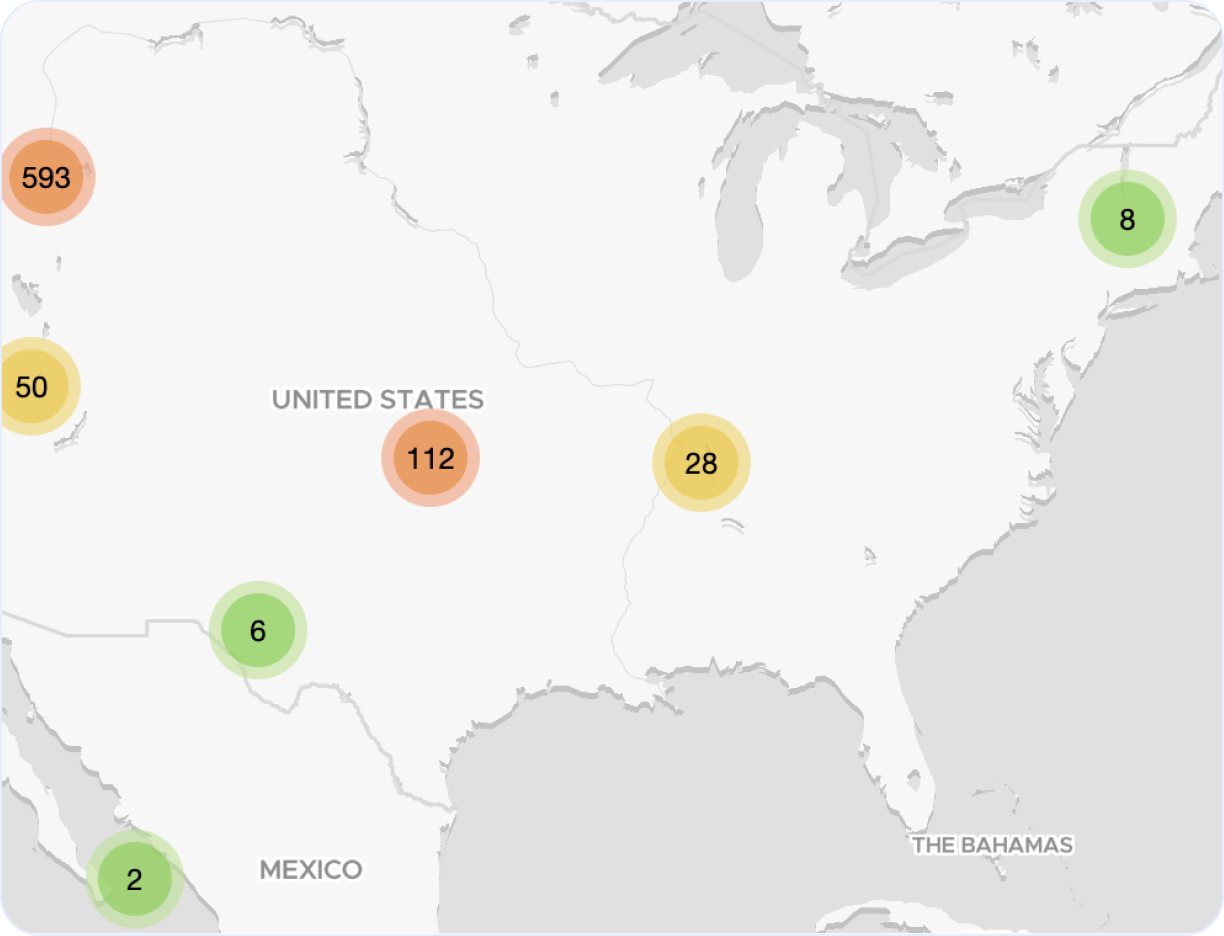
Google Cloud Functions outage map
Explore our interactive Google Cloud Functions outage map to monitor real-time incidents and service issues across the globe. This dynamic map highlights regions around the world affected by recent Google Cloud outages, giving you a clear view of performance and downtime trends.
Top reported Google Cloud outage locations, last 24 hours:
- Romania
Recently detected Google Cloud outages
| Incident description | Duration | StatusGator detected | Officially acknowledged |
|---|---|---|---|
| Google App Engine console unavailable | 4h 30m |
Never acknowledged
|
|
| BigQuery service outage | 34m |
Never acknowledged
|
|
| Gemini API and Vertex AI service outage | 1h 2m |
Never acknowledged
|
|
| Cloud Build jobs failing to start or stuck in queue | 19m |
Never acknowledged
|
|
| Locker Studio not loading | 2h 35m |
Never acknowledged
|
|
| Query results not displaying and error messages appearing | 38m |
Never acknowledged
|
|
| Looker Studio experiencing system errors and not loading charts | 1h 54m |
Never acknowledged
|
|
| Service connectivity and performance issues | 51m |
Never acknowledged
|
|
| Issues connecting to AppSheet. | 58m |
Never acknowledged
|
|
| Issues with Looker Studio dashboard loading and data retrieval | 5h 14m |
Never acknowledged
|
Looking to track Google Cloud Functions downtime and outages?
- Receive real-time status updates
- Show current status on private or public status page
- Be the first to know if service is down
- Keep your team informed
- Monitor alongside other services and websites
Recent Google Cloud Functions outages and issues
| Incident Name | Duration | Started | Severity |
|---|---|---|---|
|
Mandiant Managed Defense is experiencing issues with ingestion of some alerts from CrowdStrike integrations.
|
1m |
Warn
|
|
|
Mandiant Managed Defense is experiencing issues with ingestion of some alerts from CrowdStrike integrations.
|
598d 11h 5m |
Warn
|
|
|
Increased latency and error rates observed on Google App Engine and Google Cloud Functions gen 1. and Mandiant Managed Defense is experiencing issues with ingestion of some alerts from CrowdStrike integrations.
|
1m |
Down
|
|
|
Increased latency and error rates observed on Google App Engine and Google Cloud Functions gen 1. and Mandiant Managed Defense is experiencing issues with ingestion of some alerts from CrowdStrike integrations.
|
55m |
Down
|
|
|
Global: Multiple Cloud Products Experiencing Deployment Failures
|
1m |
Warn
|
Get notified about Google Cloud Functions outages
Stay updated with instant alerts for Google Cloud Functions outages by signing up now!
See Google Cloud Functions status on your status page
You can also monitor any service or website on your status page
Get notified about Google Cloud Functions outages
Stay updated with instant alerts for Google Cloud Functions outages by signing up now!
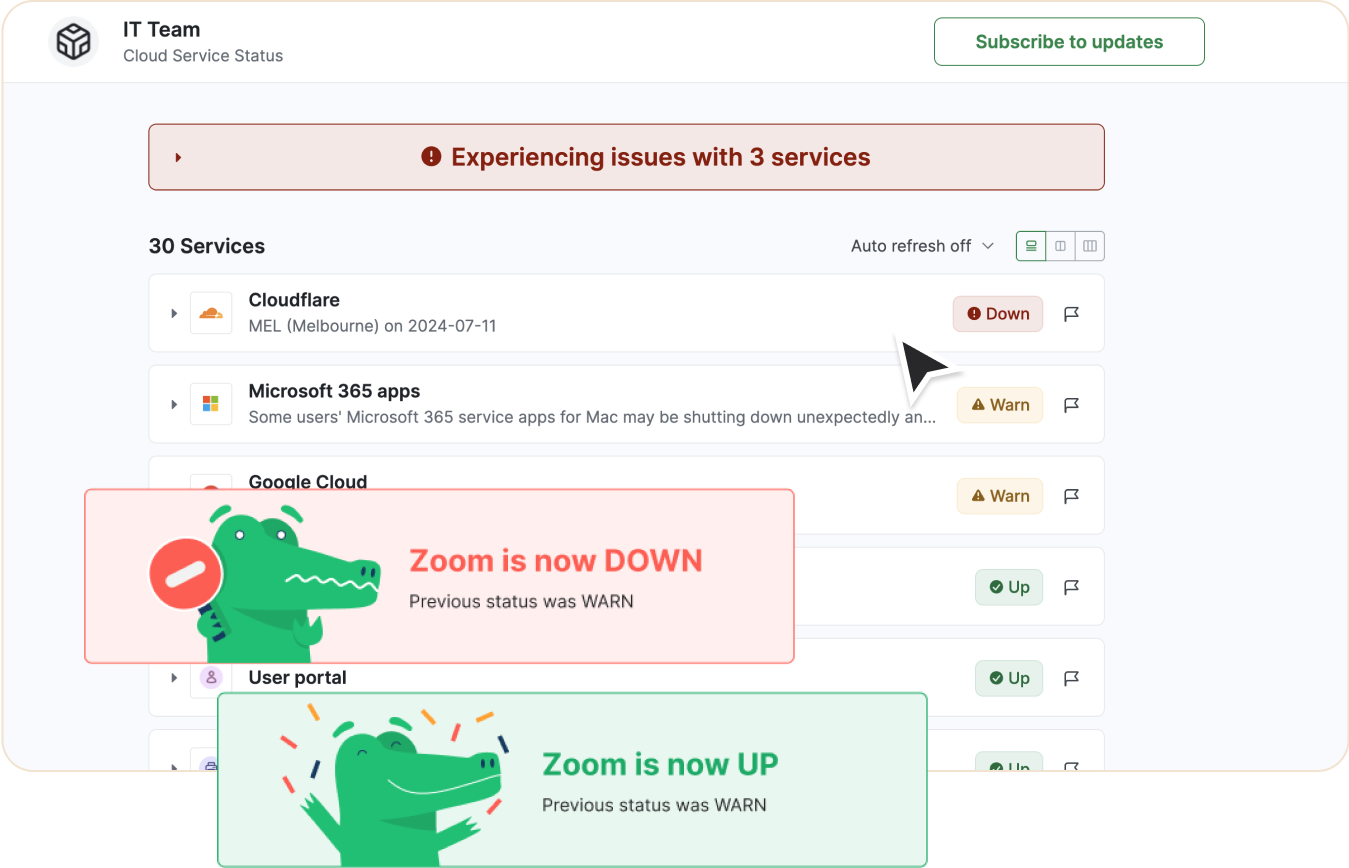
One App that has it all
With features designed to cover all your needs for monitoring and communicating outages or downtime, StatusGator keeps your team connected and informed. Stay updated on Google Cloud Functions outages, potential problems, and its current status in real-time, ensuring you're always prepared to act.
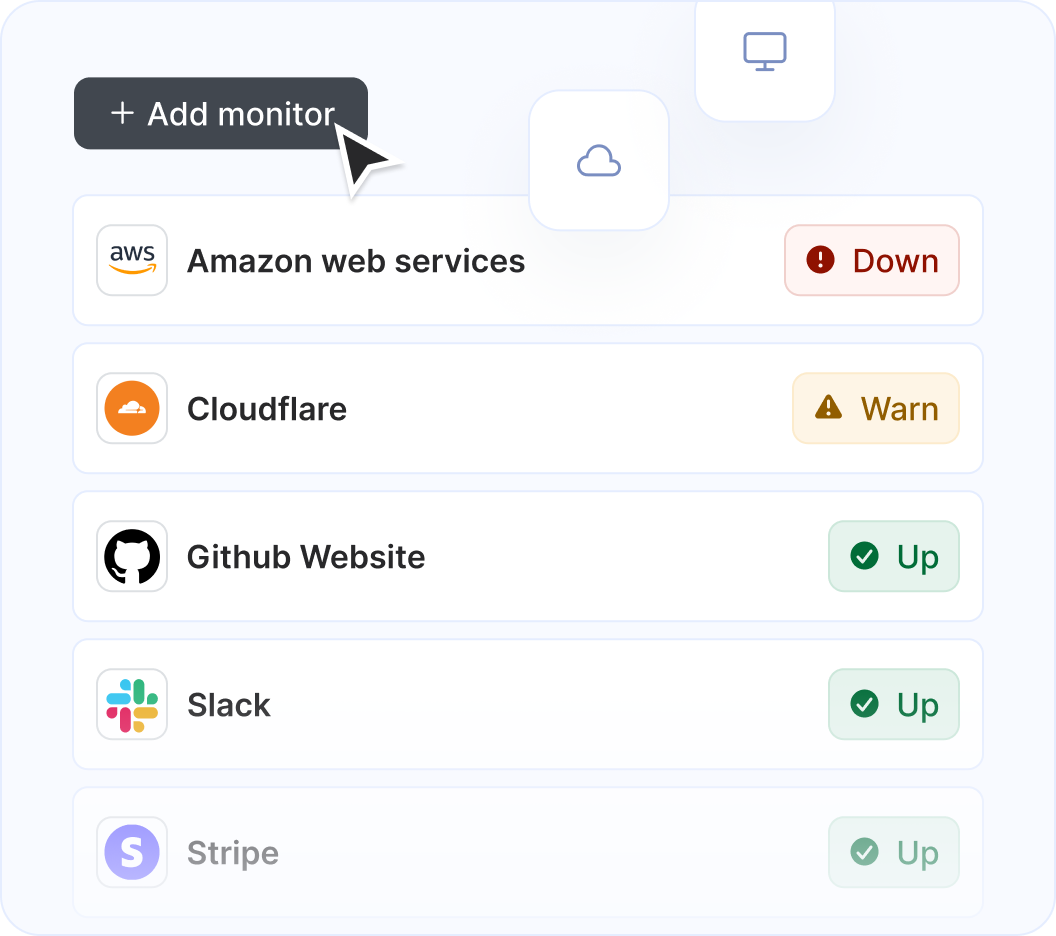
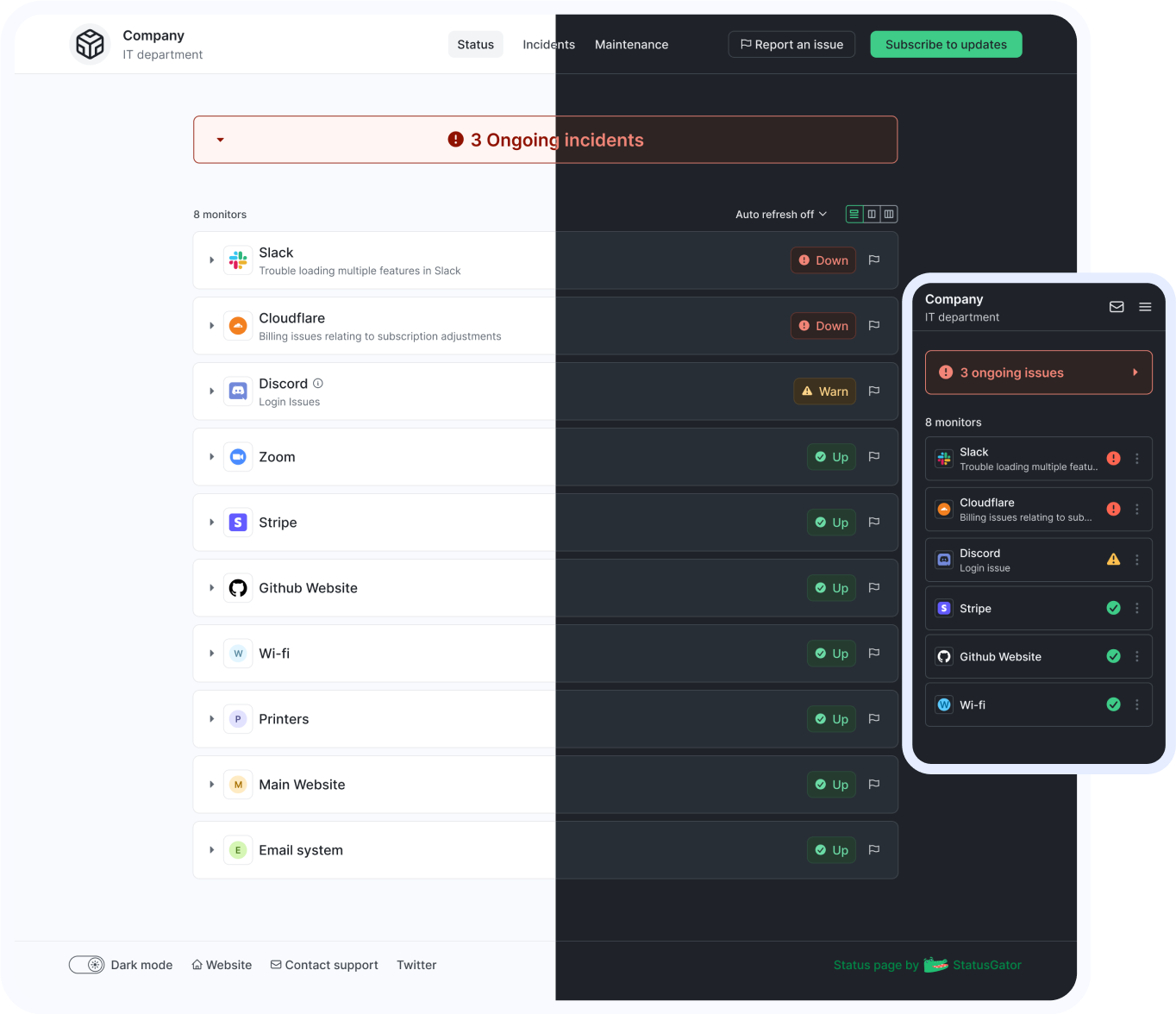
Monitor Google Cloud Functions along with other services and websites
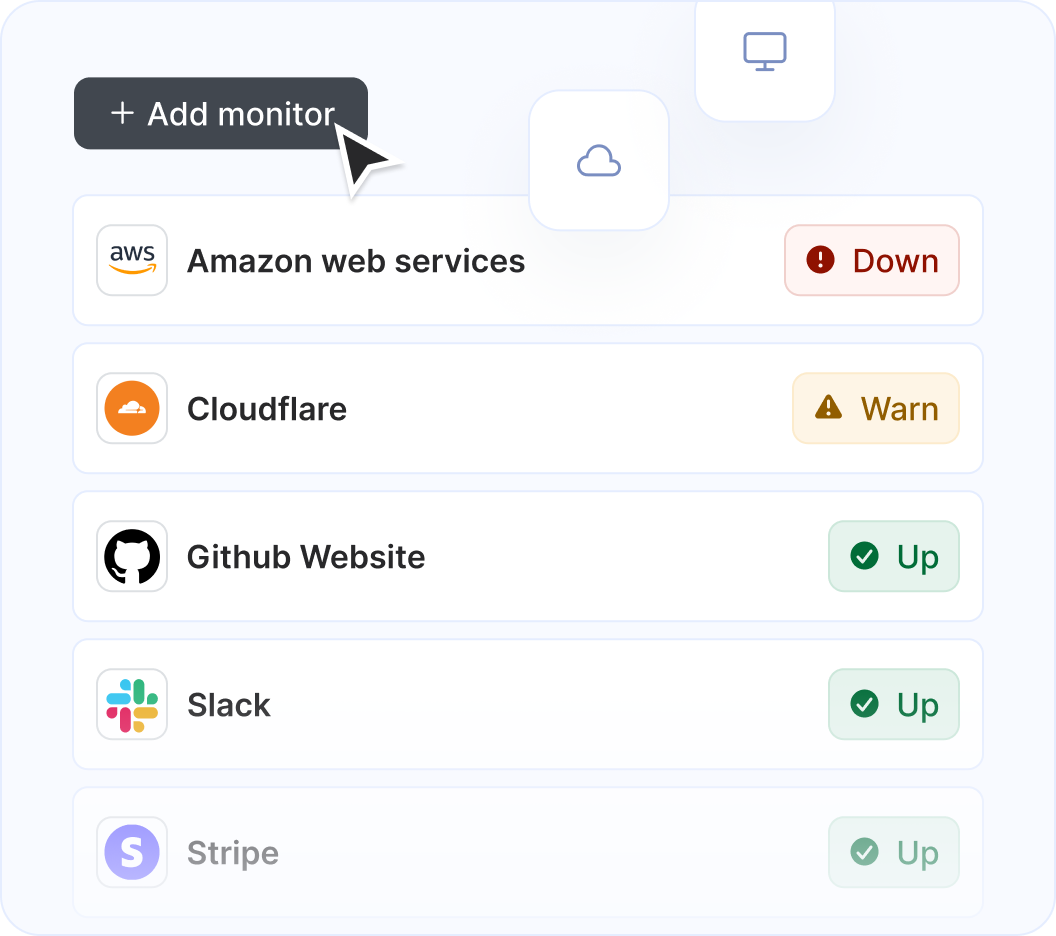
StatusGator monitors over 8,260 cloud services, hosted applications, and websites. Just add what you need to the list, and we'll automatically aggregate their statuses into a single page. You'll receive notifications for any issues affecting you and your page subscribers.
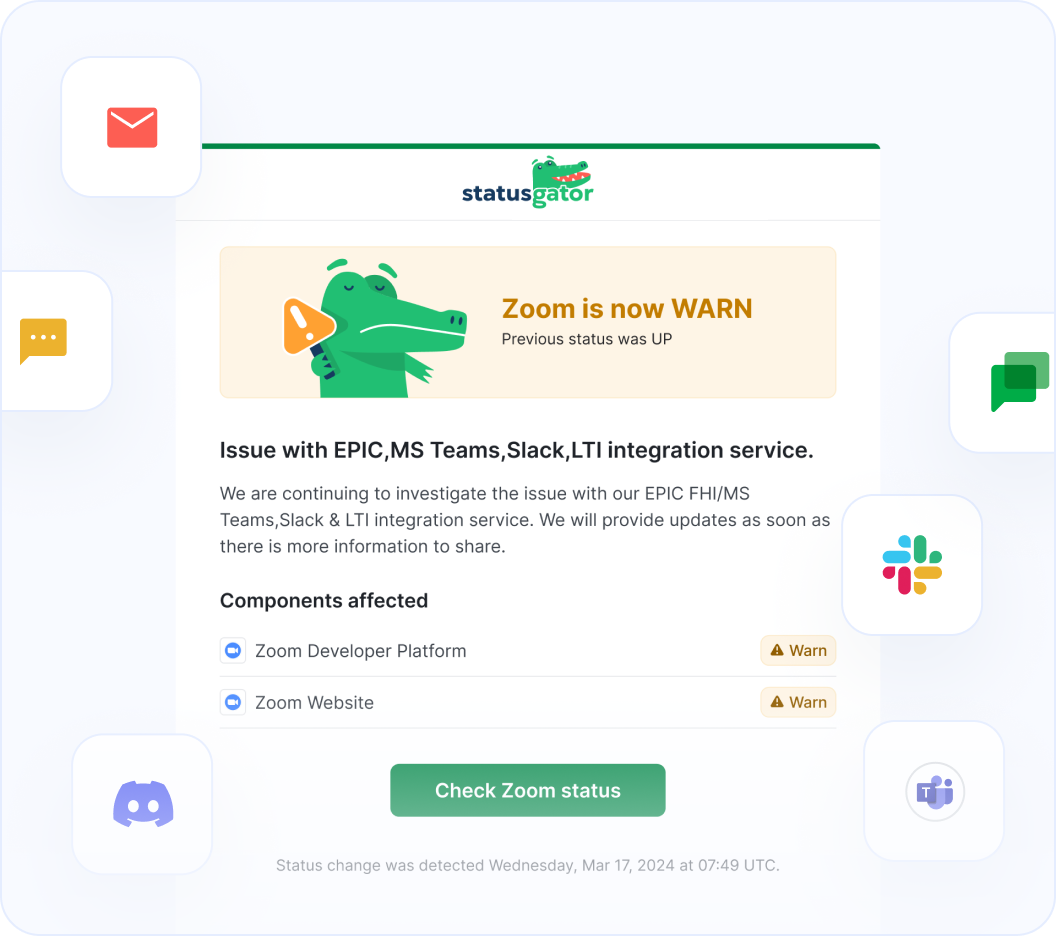
Get notified on Google Cloud Functions status change
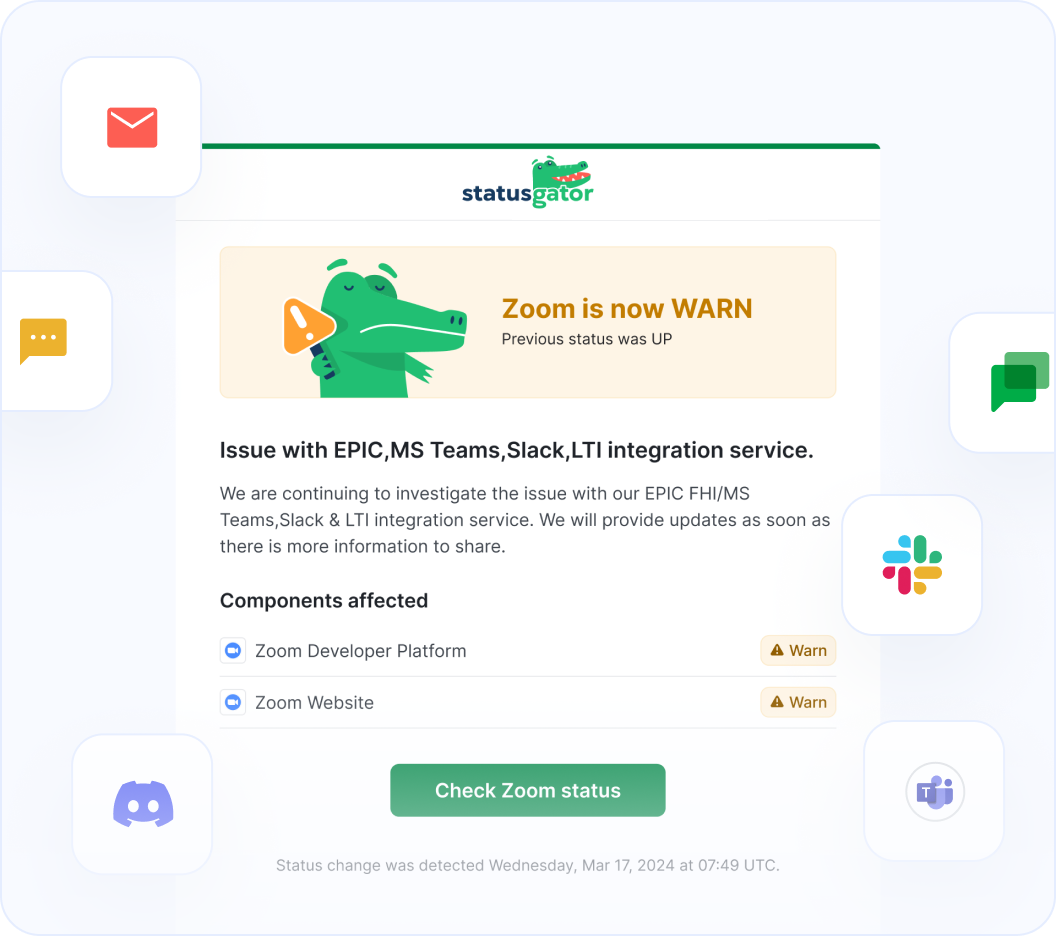
StatusGator monitors all of your services and websites and sends your team instant notifications when they go down. Stay abreast of issues that affect your team with notifications: in email, Slack, Teams, or wherever your team communicates.
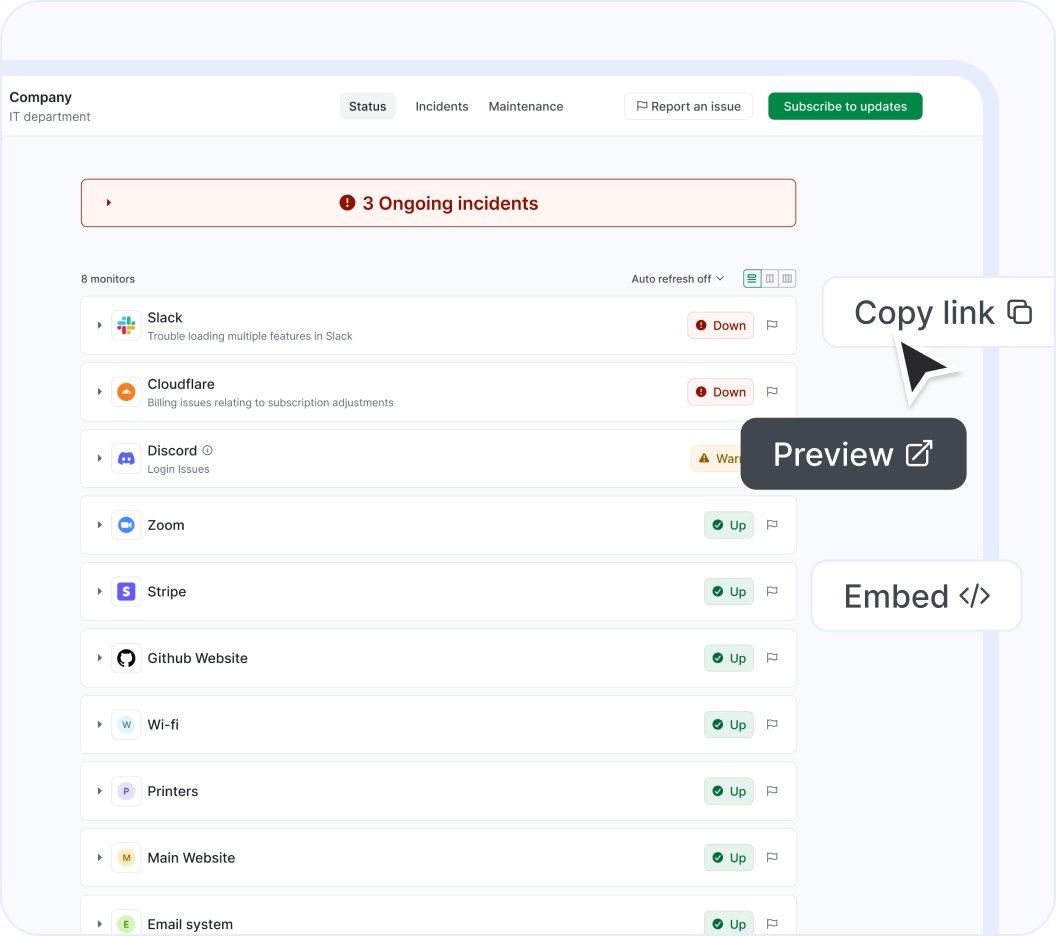
Show Google Cloud Functions on your status page
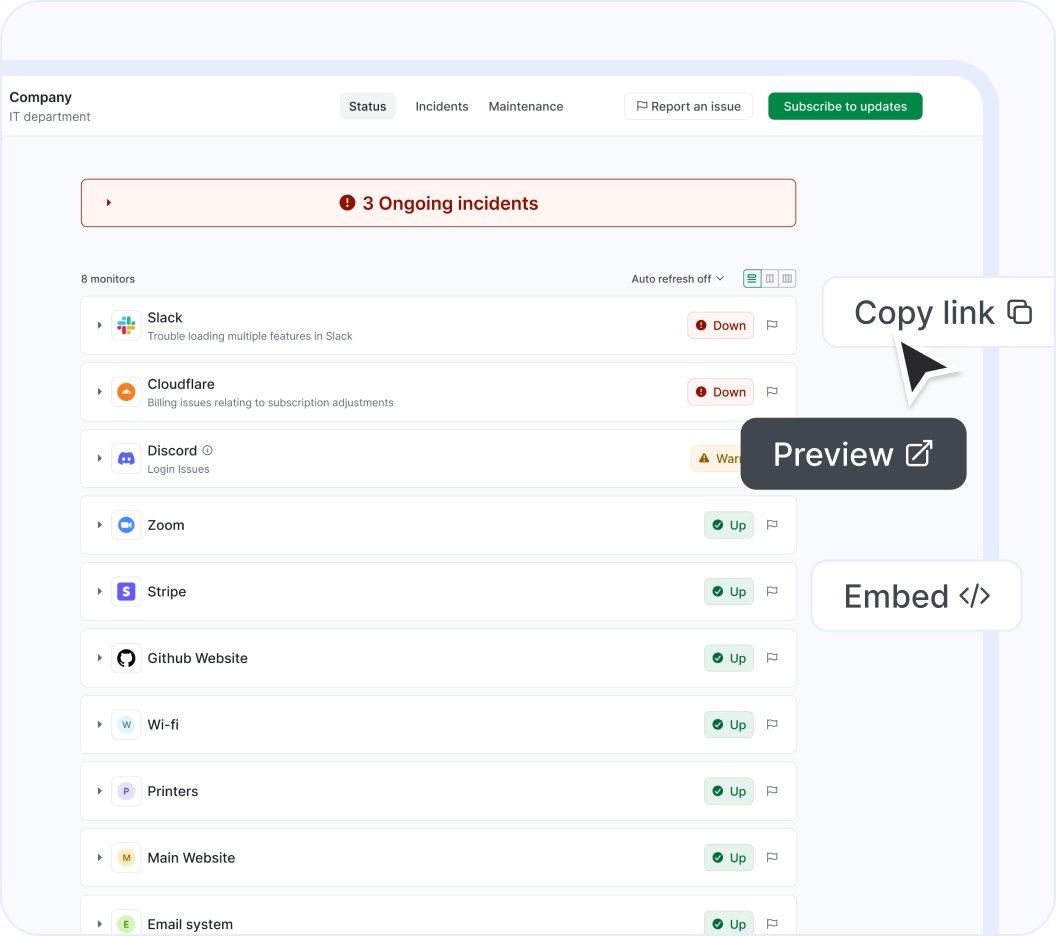
Easily notify your end-users of outages using a customizable status page. Display cloud services or websites, as well as any custom monitors you add manually. Create multiple status pages tailored to different needs, customize them, and embed them for maximum effectiveness.
Users who monitor Google Cloud Functions status also follow these services
About our Google Cloud Functions status page integration
Google Cloud Functions (Cloud computing services for business challenges by Google Cloud) is a a Cloud Infrastructure solution that StatusGator has been monitoring since August 2016. Over the past over 9 years, we have collected data on on more than 2,611 outages that affected Google Cloud Functions users. When Google Cloud Functions publishes downtime on their status page, they do so across 7,909 components and 71 groups using 3 different statuses: up, warn, and down which we use to provide granular uptime metrics and notifications.
If you're wondering, "Is Google Cloud Functions down?", or need to know its current status, we've got you covered. Our platform tracks every reported outage, performance issue, and maintenance window to ensure you're informed. Whether Google Cloud Functions is experiencing a problem now or has recently resolved one, our detailed history keeps you updated.
More than 2,800 StatusGator users monitor Google Cloud Functions to get notified when it's down or has an outage. This makes it one of the most popular Cloud Infrastructure services monitored on our platform. We've sent more than 448,200 notifications to our users about Google Cloud Functions incidents, providing transparency and peace of mind. You can get alerts by signing up for a free StatusGator account.
-
Early Warning Signals
If we detect a potential Google Cloud Functions outage or other issue before it was reported on the official status page we will send an Early Warning Signal notification to StatusGator subscribers. We can often detect issues before they are officially acknowledged by the provider, giving you a head start on resolving any potential problems.
-
Down Notifications
If Google Cloud Functions is having system outages or experiencing other critical issues, red down notifications appear on the status page. In most cases, it means that core functions are not working properly, or there is some other serious customer-impacting event underway.
-
Warning Notifications
Warn notifications are used when Google Cloud Functions is undergoing a non-critical issue like minor service issues, performance degradation, non-core bugs, capacity issues, or problems affecting a small number of users.
-
Maintenance Notifications
Google Cloud Functions does not post separate notifications for planned maintenance work so we are unable to send notifications when maintenance windows begin. If you need Google Cloud Functions maintenance notifications, please email us.
-
Status Messages
When Google Cloud Functions posts issues on their status page, we collect the main headline message and include that brief information or overview in notifications to StatusGator subscribers.
-
Status Details
When Google Cloud Functions has outages or other service-impacting events on their status page, we pull down the detailed informational updates and include them in notifications. These messages often include the current details about how the problem is being mitigated, or when the next update will occur.
-
Component Status Filtering
Because Google Cloud Functions has several components, each with their individual statuses, StatusGator can differentiate the status of each component in our notifications to you whenever a particular component is down. This means, you can filter your status page notifications based on the services, regions, or components you utilize. This is an essential feature for complex services with many components or services spread out across many regions.
Get notified about Google Cloud Functions outages
Stay updated with instant alerts for Google Cloud Functions outages by signing up now!
Looking for Downdetector Google Cloud Functions alerts?
Frequently asked questions
Can't find your question? Email us to arrange a time to discuss. We'd love to chat!