StatusGator analysis identifies 92 cloud services that publicly acknowledged disruptions tied to the AWS Middle East incident.
Over the weekend, Amazon confirmed that drone strikes damaged AWS facilities in the Middle East, disrupting cloud infrastructure across the region.
The strikes affected AWS regions in the United Arab Emirates and Bahrain, causing outages and degraded performance across core cloud services including compute, storage, and databases.
Much of the media coverage has focused on the geopolitical implications of the incident. But the larger story for cloud users is the downstream impact across the cloud ecosystem.
At StatusGator, we analyzed outage reports across thousands of cloud platforms to answer a key question “Which services were actually affected?”
Our analysis identified 92 SaaS and cloud services that publicly acknowledged disruptions tied to the AWS Middle East incident.
What happened to AWS infrastructure
According to updates posted on the AWS Service Health Dashboard, the incident involved physical damage to multiple AWS facilities.
AWS reported:
“Due to the ongoing conflict in the Middle East, both affected regions have experienced physical impacts to infrastructure as a result of drone strikes. In the UAE, two of our facilities were directly struck, while in Bahrain, a drone strike in close proximity to one of our facilities caused physical impacts to our infrastructure.”
The outages affected two AWS regions:
| Region | Location | Impact |
|---|---|---|
| me-central-1 | Dubai, UAE | Two Availability Zones (data centers) impaired |
| me-south-1 | Askar, Bahrain | Infrastructure damage near facility |
AWS regions are composed of multiple Availability Zones (AZs). Each AZ typically represents one or more physical data centers with independent power, cooling, and networking.
A single AZ failure normally does not cause major outages. But in this case, multiple facilities sustained physical damage, creating widespread capacity constraints and service degradation.
AWS reported elevated error rates across services including:
- EC2
- S3
- Lambda
- DynamoDB
- RDS
- CloudWatch
- Kinesis
Major media outlets including CNBC and Reuters also reported that three AWS facilities were affected across the two regions.
Timeline of the AWS Middle East Incident
The following timeline reconstructs the event based on AWS service health updates and status reports from affected cloud providers monitored by StatusGator.
March 1, 2026 00:40 UTC: Initial provider incidents begin appearing referencing disruptions affecting AWS infrastructure in the Middle East.
March 1, 2026 ~02:00 UTC: AWS acknowledges infrastructure disruption affecting the me-central-1 (UAE) and me-south-1 (Bahrain) regions.
March 1, 2026 ~04:30 UTC: AWS confirms that multiple facilities experienced physical impacts from drone strikes, including two facilities in the UAE and infrastructure damage near a Bahrain facility.
March 1, 2026 ~06:00 UTC: AWS reports elevated error rates across multiple core services including EC2, S3, Lambda, DynamoDB, and RDS.
March 1, 2026: 08:00–12:00 UTC Cloud providers begin publishing status updates linking service degradation to AWS infrastructure disruptions in the Middle East.
Affected providers report: degraded APIs, delayed background jobs, increased latency, messaging failures
March 1, 2026 ~16:00 UTC: Several providers report rerouting traffic to alternate regions in Europe and Asia as AWS capacity constraints continue.
March 2, 2026 ~03:00 UTC: AWS reports gradual restoration of capacity as damaged infrastructure is isolated and workloads are redistributed.
March 2, 2026 08:00–18:00 UTC: Providers begin resolving incidents as failover systems stabilize and AWS services recover.
StatusGator analysis: 92 services impacted
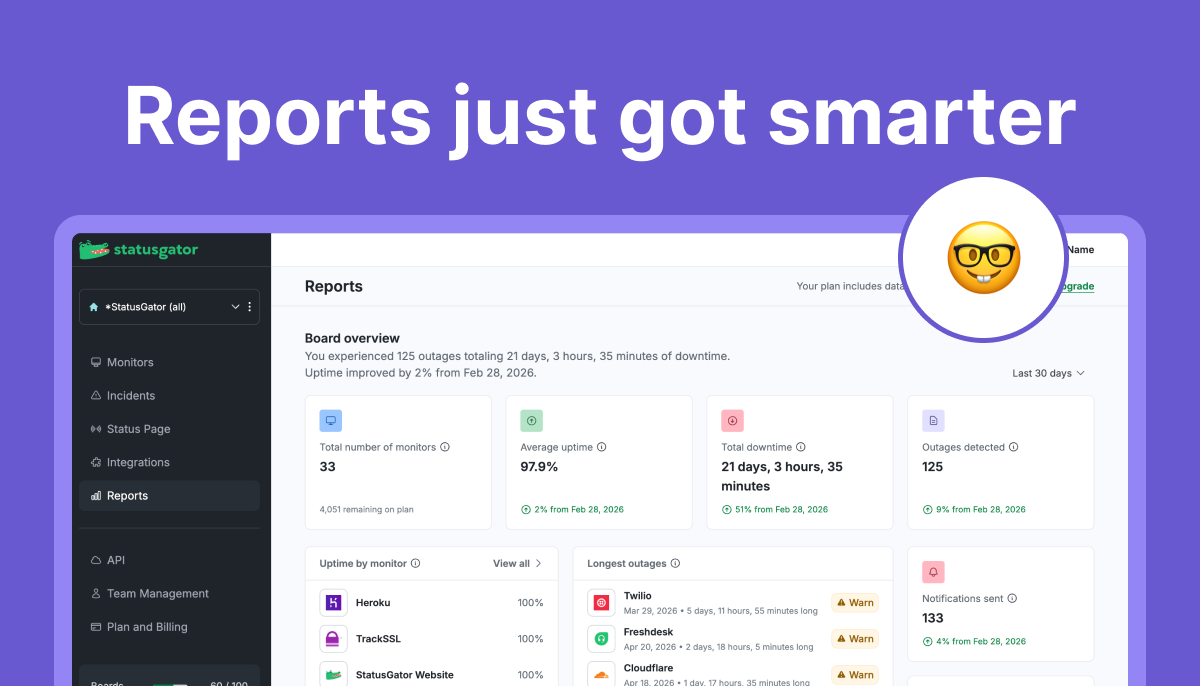
StatusGator continuously monitors the status pages of more than 7,000 cloud services and SaaS platforms.
Our system tracks provider status updates in real time, allowing us to detect when outages cascade across the cloud ecosystem.
To analyze the AWS incident, we searched our outage database for providers that publicly referenced:
- AWS Middle East regions
- me-central-1
- me-south-1
- UAE infrastructure failures
- Bahrain region outages
We identified 92 services that publicly acknowledged disruptions tied to the AWS Middle East incident.
Because StatusGator aggregates status reports across thousands of providers, we are uniquely positioned to quantify how infrastructure outages propagate across the cloud ecosystem.
Categories of services affected
The impacted services span a wide range of cloud software categories.
Security platforms
Security services were heavily affected because many run globally distributed inspection and gateway infrastructure.
Examples include:
- Palo Alto Networks
- Prisma by Palo Alto
- Check Point
- Cisco Secure Access
- FortiSASE
- Wiz
- Menlo Security
- ThreatLocker
Data infrastructure
Several major database and analytics platforms reported issues.
Examples include:
Developer platforms
Tools used by engineering teams also experienced disruptions.
Examples include:
SaaS applications
Several widely used business applications reported regional disruptions.
Examples include:
Communications platforms
Telecommunications APIs and messaging services were also affected.
Examples include:
In total, StatusGator identified 92 impacted services across more than a dozen cloud software categories.
Notable service disruptions
Below are some of the most notable providers that publicly acknowledged disruptions tied to the AWS Middle East incident.
Vercel
Vercel confirmed disruptions affecting deployments and edge infrastructure serving the Middle East region.
The company reported degraded performance tied to AWS infrastructure issues in affected regions. Some applications experienced increased latency until traffic could be rerouted.
Because Vercel powers a large number of frontend deployments and serverless applications, the disruption likely affected a wide range of websites and applications indirectly.
Slack
Slack reported degraded service for organizations using Dubai-based data residency.
Users in the region experienced search failures and degraded search performance after AWS infrastructure damage made some underlying data shards temporarily unreachable.
Slack said the issue stemmed from a severe physical infrastructure incident affecting AWS facilities, which disrupted access to older files and database records stored in the region.
Messaging services remained operational, but search functionality for Dubai-hosted data remained impaired while engineers worked with AWS to restore affected storage infrastructure.
Asana
Asana reported degraded performance affecting customers served from AWS infrastructure in the Middle East.
The issue impacted task updates and application responsiveness for some users until failover mechanisms stabilized service.
Redis
Redis reported service disruption tied to infrastructure issues affecting AWS Middle East regions.
Because Redis is commonly used as a caching layer and real-time data store, outages can quickly impact application responsiveness and performance.
Datadog
Datadog integrations referencing AWS infrastructure reported degraded monitoring capabilities in affected regions.
Monitoring pipelines and metrics ingestion experienced delays as AWS services experienced instability.
MongoDB Cloud
MongoDB Cloud reported regional service degradation affecting clusters hosted in impacted AWS regions.
Database operations experienced elevated latency until infrastructure availability stabilized.
Snowflake
Snowflake acknowledged service disruption tied to AWS infrastructure in the Middle East.
Some workloads experienced query delays and connectivity issues as the underlying cloud infrastructure degraded.
Twilio
Twilio reported messaging and communications disruptions affecting traffic routed through infrastructure serving the Middle East.
Developers relying on Twilio APIs for messaging and voice experienced intermittent failures during the incident.
Prisma by Palo Alto
Prisma by Palo Alto reported issues affecting inspection services connected to impacted AWS regions.
Organizations relying on Prisma gateways experienced degraded connectivity until services stabilized.
Wiz
Wiz reported disruptions affecting visibility and scanning workloads in affected regions.
Infrastructure degradation impacted some customers’ security monitoring pipelines.
Full List of Affected Services
StatusGator identified 92 providers that publicly acknowledged disruptions tied to the AWS Middle East incident.
Examples include:
- Amazon Web Services
- Snowflake
- MongoDB
- Slack
- Asana
- Vercel
- Redis
- Datadog
- Twilio
- Palo Alto Networks
- Check Point
- Cisco Secure Access
- Wiz
- Dynatrace
- Grafana
- JFrog
- Qlik
- Sprinklr
- UXCam
- Slido
- Cohesity
- ClickHouse
- CloudAMQP
(Full dataset available to journalists upon request.)
Why StatusGator can quantify cloud outage impact
StatusGator monitors the status pages of more than 7,000 cloud services and SaaS providers.
Our platform continuously tracks:
- provider status pages
- incident updates
- historical outages
- service degradation reports
Because many SaaS companies rely on shared cloud infrastructure, outages at hyperscale providers often propagate across dozens of downstream platforms.
StatusGator’s dataset allows us to quantify how outages spread across the cloud ecosystem.
In the case of the AWS Middle East incident, this analysis revealed 92 providers reporting disruptions linked to the infrastructure damage.